We just finished our 9th annual Hacking for Defense class at Stanford.
What a year.
Hacking for Defense, now in 60 universities, has teams of students working to understand and help solve national security problems. At Stanford this quarter the 8 teams of 40 students collectively interviewed 968 beneficiaries, stakeholders, requirements writers, program managers, industry partners, etc. – while simultaneously building a series of minimal viable products and developing a path to deployment.
At the end of the quarter, each of the teams gave a final “Lessons Learned” presentation. Unlike traditional demo days or Shark Tanks which are, “Here’s how smart I am, and isn’t this a great product, please give me money,” the Lessons Learned presentations tell the story of each team’s 10-week journey and hard-won learning and discovery. For all of them it’s a roller coaster narrative describing what happens when you discover that everything you thought you knew on day one was wrong and how they eventually got it right.
Here’s how they did it and what they delivered.
New for 2024
This year, in addition to the problems from the Defense Department and Intelligence Community we had two problems from the State Department and one from the FBI.
These are “Wicked” Problems
Wicked problems refer to really complex problems, ones with multiple moving parts, where the solution isn’t obvious and lacks a definitive formula. The types of problems our Hacking For Defense students work on fall into this category. They are often ambiguous. They start with a problem from a sponsor, and not only is the solution unclear but figuring out how to acquire and deploy it is also complex. Most often students find that in hindsight the problem was a symptom of a more interesting and complex problem – and that Acquistion of solutions in the Dept of Defense is unlike anything in the commercial world.
 And the stakeholders and institutions often have different relationships with each other – some are collaborative, some have pieces of the problem or solution, and others might have conflicting values and interests.
And the stakeholders and institutions often have different relationships with each other – some are collaborative, some have pieces of the problem or solution, and others might have conflicting values and interests.
The figure shows the types of problems Hacking for Defense students encounter, with the most common ones shaded.
Guest Speakers: Doug Beck – Defense Innovation Unit, Radha Plumb – CDAO. H.R. McMaster – former National Security Advisor and Condoleezza Rice – former Secretary of State
Our final Lessons Learned presentations started with an introduction by Doug Beck, director of the Defense Innovation Unit and Radha Plumb, DoD’s Chief of the Digital and AI Office– reminding the students of the importance of Hacking for Defense and congratulating them on their contribution to national security.
H.R. McMaster gave an inspiring talk. He reminded our students that 1) war is an extension of politics; 2) war is human; 3) war is uncertain; 4) war is a contest of wills.
If you can’t see the video of H.R. McMaster’s talk, click here.
The week prior to our final presentations the class heard inspirational remarks from Dr. Condoleezza Rice, former United States Secretary of State. Dr. Rice gave a sweeping overview of the prevailing threats to our national security and the importance of getting our best and brightest involved in public service.
As a former Secretary of State, Dr. Rice was especially encouraged to see our two State Department sponsored teams this quarter. She left the students inspired to find ways to serve.
Lessons Learned Presentation Format
For the final Lessons Learned presentation many of the eight teams presented a 2-minute video to provide context about their problem. This was followed by an 8-minute slide presentation describing their customer discovery journey over the 10 weeks. While all the teams used the Mission Model Canvas, (videos here), Customer Development and Agile Engineering to build Minimal Viable Products, each of their journeys was unique.
By the end the class all the teams realized that the problem as given by the sponsor had morphed into something bigger, deeper and much more interesting.
All the presentations are worth a watch.
Team House of Laws
Using LLMs to Simplify Government Decision Making
If you can’t see the Team House of Laws 2-minute video, click here
 If you can’t see the Team House of Laws slides, click here
If you can’t see the Team House of Laws slides, click here
Mission-Driven Entrepreneurship
This class is part of a bigger idea – Mission-Driven Entrepreneurship. Instead of students or faculty coming in with their own ideas, we ask them to work on societal problems, whether they’re problems for the State Department or the Department of Defense or non-profits/NGOs or the Oceans and Climate or for anything the students are passionate about. The trick is we use the same Lean LaunchPad / I-Corps curriculum — and the same class structure – experiential, hands-on– driven this time by a mission-model not a business model. (The National Science Foundation and the Common Mission Project have helped promote the expansion of the methodology worldwide.)
Mission-driven entrepreneurship is the answer to students who say, “I want to give back. I want to make my community, country or world a better place, while being challenged to solve some of the toughest problems.”
Caribbean Clean Climate
Helping Barbados Adopt Clean Energy
If you can’t see the Caribbean Clean Climate 2-minute video, click here
 If you can’t see the Caribbean Clean Climate slides, click here
If you can’t see the Caribbean Clean Climate slides, click here
It Started With An Idea
Hacking for Defense has its origins in the Lean LaunchPad class I first taught at Stanford in 2011. I observed that teaching case studies and/or how to write a business plan as a capstone entrepreneurship class didn’t match the hands-on chaos of a startup. Furthermore, there was no entrepreneurship class that combined experiential learning with the Lean methodology. Our goal was to teach both theory and practice.
The same year we started the class, it was adopted by the National Science Foundation to train Principal Investigators who wanted to get a federal grant for commercializing their science (an SBIR grant.) The NSF observed, “The class is the scientific method for entrepreneurship. Scientists understand hypothesis testing” and relabeled the class as the NSF I-Corps (Innovation Corps). I-Corps became the standard for science commercialization for the National Science Foundation, National Institutes of Health and the Department of Energy, to date training 3,051 teams and launching 1,300+ startups.
Team Protecting Children
Helping the FBI Acquire LLMs for Child Safety
If you can’t see the Team Protecting Children 2-minute video, click here
 If you can’t see the Team Protecting Children slides, click here
If you can’t see the Team Protecting Children slides, click here
Origins Of Hacking For Defense
In 2016, brainstorming with Pete Newell of BMNT and Joe Felter at Stanford, we observed that students in our research universities had little connection to the problems their government was trying to solve or the larger issues civil society was grappling with. As we thought about how we could get students engaged, we realized the same Lean LaunchPad/I-Corps class would provide a framework to do so. That year we launched both Hacking for Defense and Hacking for Diplomacy (with Professor Jeremy Weinstein and the State Department) at Stanford. The Department of Defense adopted and scaled Hacking for Defense across 60 universities while Hacking for Diplomacy is offered at JMU and RIT –, sponsored by the Department of State Bureau of Diplomatic Security (see here).
Team L Infinity
Improving Satellite Tasking
If you can’t see the Team L∞ 2-minute video, click here
 If you can’t see the Team L∞ slides, click here
If you can’t see the Team L∞ slides, click here
Goals for the Hacking for Defense Class
Our primary goal was to teach students Lean Innovation methods while they engaged in national public service. Today if college students want to give back to their country, they think of Teach for America, the Peace Corps, or AmeriCorps or perhaps the US Digital Service or the GSA’s 18F. Few consider opportunities to make the world safer with the Department of Defense, Intelligence community or other government agencies.
In the class we saw that students could learn about the nation’s threats and security challenges while working with innovators inside the DoD and Intelligence Community. At the same time the experience would introduce to the sponsors, who are innovators inside the Department of Defense (DOD) and Intelligence Community (IC), a methodology that could help them understand and better respond to rapidly evolving threats. We wanted to show that if we could get teams to rapidly discover the real problems in the field using Lean methods, and only then articulate the requirements to solve them, defense acquisition programs could operate at speed and urgency and deliver timely and needed solutions.
Finally, we wanted to familiarize students with the military as a profession and help them better understand its expertise, and its proper role in society. We hoped it would also show our sponsors in the Department of Defense and Intelligence community that civilian students can make a meaningful contribution to problem understanding and rapid prototyping of solutions to real-world problems.
Team Centiment
Information Operations Optimized
If you can’t see the Team Centiment 2-minute video, click here
 If you can’t see the Team Centiment slides, click here
If you can’t see the Team Centiment slides, click here
Mission-Driven in 50 Universities and Continuing to Expand in Scope and Reach
What started as a class is now a movement.
From its beginning with our Stanford class, Hacking for Defense is now offered in over 50 universities in the U.S., as well as in the UK and Australia. Steve Weinstein started Hacking for Impact (Non-Profits) and Hacking for Local (Oakland) at U.C. Berkeley, and Hacking for Oceans at both Scripps and UC Santa Cruz, as well as Hacking for Climate and Sustainability at Stanford. Hacking for Education will start this fall at Stanford.
Team Guyana’s Green Growth
Water Management for Guyanese Farmers
If you can’t see the Team Guyana’s Green Growth 2-minute video, click here
 If you can’t see the Team Guyana’s Green Growth slides, click here
If you can’t see the Team Guyana’s Green Growth slides, click here
Go-to-Market/Deployment Strategies
The initial goal of the teams is to ensure they understand the problem. The next step is to see if they can find mission/solution fit (the DoD equivalent of commercial product/market fit.) But most importantly, the class teaches the teams about the difficult and complex path of getting a solution in the hands of a warfighter/beneficiary. Who writes the requirement? What’s an OTA? What’s color of money? What’s a Program Manager? Who owns the current contract? …
Team Dynamic Space Operations
Cubesats for Space Inspection Training
If you can’t see the Team Dynamic Space Operations 2-minute video, click here
 If you can’t see the Team Dynamic Space Operations slides, click here
If you can’t see the Team Dynamic Space Operations slides, click here
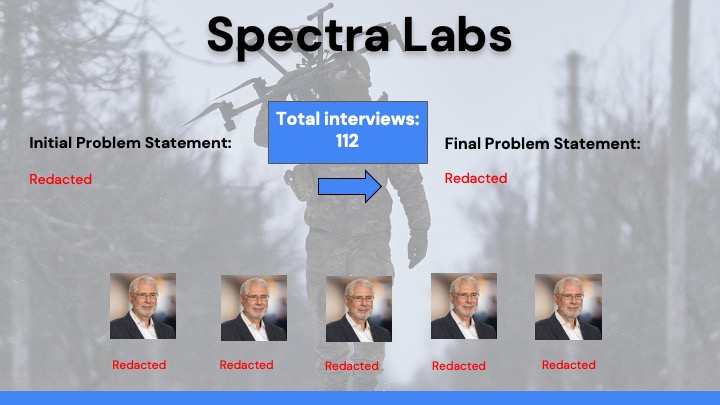
Team Spectra Labs
Providing real-time awareness of ..
This team’s presentation is available upon request.
If you can’t see the Spectra Labs slides, click here
What’s Next For These Teams?
When they graduate, the Stanford students on these teams have the pick of jobs in startups, companies, and consulting firms. House of Laws got accepted and has already started at Y-Combinator. L-Infinity, Dynamics Space Operations team (now Juno Astrodynamics,) and Spectra Labs are started work this week at H4X Labs, an accelerator focused on building dual-use companies that sell to both the government and commercial firms. Many of the teams will continue to work with their problem sponsor. Several will join the Stanford Gordian Knot Center for National Security Innovation which is focused on the intersection of policy, operational concepts, and technology.
In our post class survey 86% of the students said that the class had impact on their immediate next steps in their career. Over 75% said it changed their opinion of working with the Department of Defense and other USG organizations.
It Takes A Village
While I authored this blog post, this class is a team project. The secret sauce of the success of Hacking for Defense at Stanford is the extraordinary group of dedicated volunteers supporting our students in so many critical ways.
The teaching team consisted of myself and:
- Pete Newell, retired Army Colonel and ex Director of the Army’s Rapid Equipping Force, now CEO of BMNT.
- Joe Felter, retired Army Colonel; and former deputy assistant secretary of defense for South Asia, Southeast Asia, and Oceania; and William J. Perry Fellow at Stanford’s Center for International Security and Cooperation.
- Steve Weinstein, partner at America’s Frontier Fund, 30-year veteran of Silicon Valley technology companies and Hollywood media companies. Steve was CEO of MovieLabs, the joint R&D lab of all the major motion picture studios. He runs H4X Labs.
- Jeff Decker, a Stanford researcher focusing on dual-use research. Jeff served in the U.S. Army as a special operations light infantry squad leader in Iraq and Afghanistan.
 Our teaching assistants this year were Joel Johnson, Malika Aubakirova, Spencer Paul, Ethan Tiao, Evan Szablowski, and Josh Pickering. A special thanks to the Defense Innovation Unit (DIU) and its National Security Innovation Network (NSIN) for supporting the program at Stanford and across the country, as well as Lockheed Martin and Northrop Grumman.
Our teaching assistants this year were Joel Johnson, Malika Aubakirova, Spencer Paul, Ethan Tiao, Evan Szablowski, and Josh Pickering. A special thanks to the Defense Innovation Unit (DIU) and its National Security Innovation Network (NSIN) for supporting the program at Stanford and across the country, as well as Lockheed Martin and Northrop Grumman.
31 Sponsors, Business and National Security Mentors
The teams were assisted by the originators of their problems – the sponsors.
Sponsors: Jackie Tame, Nate Huston, Mark Breier, Dave Wiltse, Katherine Beamer, Jeff Fields, Dave Miller, Shannon Rooney, and David Ryan.
National Security Mentors helped students who came into the class with no knowledge of the Dept of Defense, State and the FBI understand the complexity, intricacies and nuances of those organizations: Brad Boyd, Matt MacGregor, David Vernal, Alphanso “Fonz” Adams, Ray Powell, Sam Townsend, Tom Kulisz, Rich Lawson, Mark McVay, Nick Shenkin, David Arulanantham and Matt Lintker.
Business Mentors helped the teams understand if their solutions could be a commercially successful business: Katie Tobin, Marco Romani, Rafi Holtzman, Rachel Costello, Donnie Hassletine, Craig Seidel, Diane Schrader and Matt Croce.
Thanks to all!
Filed under: Corporate/Gov’t Innovation, Gordian Knot Center for National Security Innovation, Hacking For Defense |